Olá pessoal,
Boa noite!
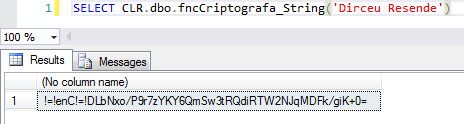
Neste post, vou demonstrar como criptografar e descriptografar senhas com o CLR (C#). Para isso, vou utilizar os algoritmos de criptografia MD5CryptoServiceProvider e TripleDESCryptoServiceProvider do .NET Framework, que permitem utilizar uma palavra-chave (Salt) para garantir que essa chave será utilizada na criptografia dos dados e somente poderá ser descriptografada utilizando essa palavra-chave secreta.
Se você não conhece o CLR e gostaria de saber mais sobre esse poderoso recurso do SQL Server, acesse este link.
Visualizar código-fonteExemplos de uso
This implementation is not part of the Windows Platform FIPS validated cryptographic algorithms
Se você compilou o seu assembly CLR em um servidor rodando o Windows Server, provavelmente você encontrará essa mensagem de erro ao tentar executar essas duas funções do post.
Msg 6522, Level 16, State 1, Line 6
A .NET Framework error occurred during execution of user-defined routine or aggregate “fncCriptografa_String”:
System.InvalidOperationException: This implementation is not part of the Windows Platform FIPS validated cryptographic algorithms.
System.InvalidOperationException:
at System.Security.Cryptography.MD5CryptoServiceProvider..ctor()
at Bibliotecas.Model.Utils.CreateDES(String key)
at UserDefinedFunctions.fncCriptografa_String(SqlString Ds_Senha)
Isso ocorre, pois os algoritmos utilizandos (MD5CryptoServiceProvider e TripleDESCryptoServiceProvider) não estão em conformidade com o padrão FIPS da Microsoft.
Esse problema é parecido com o que relatei no post SQL Server Reporting Services – Erro ao Salvar Relatório: System.InvalidOperationException This implementation is not part of the Windows Platform FIPS validated cryptographic algorithms., mas utilizarei uma solução diferente para este caso.
Para que você possa utilizar essas funções em seu servidor, vou apresentar duas soluções para resolver esse problema:
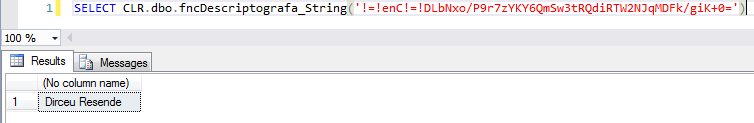
Opção 1: Desativar o FIPS
Para desativar essa configuração, basta acessar o registro do Windows, encontrar a configuração “HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa\fipsalgorithmpolicy” e alterar o valor da chave “Enabled” para 0.
Após isso, reinicie o serviço do SQL Server e você conseguirá utilizar essas funções normalmente.
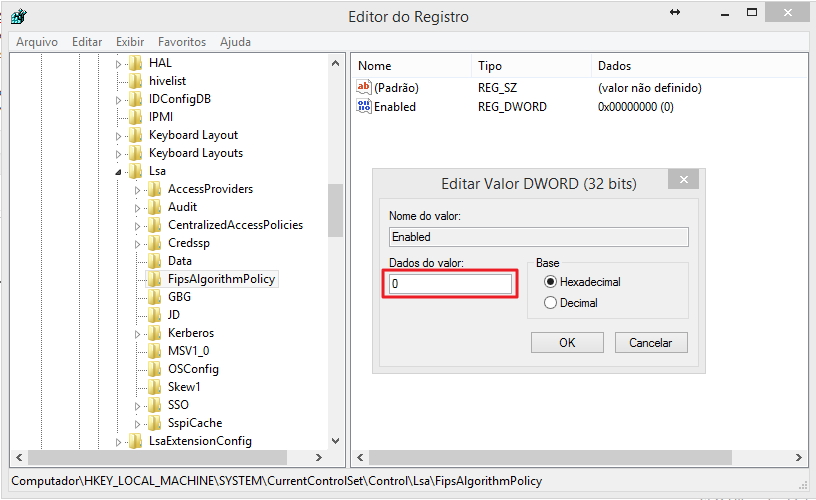
Opção 2: Alterar o arquivo sqlservr.exe.config do SQL Server
Uma forma de resolver esse problema sem precisar desativar essa política de segurança (se está ativada, provavelmente o analista de segurança da sua empresa acha que é uma boa opção) é alterando o arquivo sqlservr.exe.config, geralmente localizado em C:\Program Files\Microsoft SQL Server\MSSQL12.Nome_Da_Sua_Instancia\MSSQL\Binn e adicionar a seguinte configuração ao final do arquivo, dentro da sessão <runtime>:
|
1 |
<enforceFIPSPolicy enabled="0" /> |
O seu arquivo deverá ficar assim:
Após alterar o arquivo, reinicie o serviço do SQL Server. Essa alteração precisará ser feita em todas as instâncias onde você irá utilizar essa função.
Uma outra alternativa, é realizar essa alteração no machine.config da máquina (Geralmente localizado em C:\Windows\Microsoft.NET\Framework64\v4.0.30319\Config), mas tenha em mente que utilizando essa solução, você irá desativar essa opção para TODAS as aplicações .NET do servidor.
Algoritmos de criptografia suportados e não suportados
Veja também, a lista abaixo para identificar quais são os algoritmos suportados e quais não são pelo namespace “System.Security.Cryptography”:
Algoritmos Hash
– HMACSHA1
– MACTripleDES
– SHA1CryptoServiceProvider
Algoritmos Simétricos (Usam a mesma chave para criptografia e descriptografia)
– DESCryptoServiceProvider
– TripleDESCryptoServiceProvider
Algoritmos Assimétricos (Usam uma chave pública para criptografia e uma chave privada para descriptografia)
– DSACryptoServiceProvider
– RSACryptoServiceProvider
Algoritmos que não suportam os padrões do FIPS (e não devem ser utilizados)
– HMACMD5
– HMACRIPEMD160
– HMACSHA256
– HMACSHA384
– HMACSHA512
– MD5CryptoServiceProvider
– RC2CryptoServiceProvider
– RijndaelManaged
– RIPEMD160Managed
– SHA1Managed
And that's it, folks!
Espero que tenham gostado do post.
Um abraço e até a próxima.